|
Battling the Human Trafficking Fight - Part 2 The Social Media DangerScience & Medicine Articles May 12, 2020 by Special Guest Author - Tim Easton, Anti-Terrorism Expert (“Evil People Will Push The Limits of Evil Deeds to Feed their Sick Addiction and Greed”) tags: #social-media #diaspora #human-trafficking #battling-sex-trafficking #educatetrainprotectdefend #castledefense360 #stopchildsextrafficking #stopchildtrafficking #endhumantrafficking #stophumantrafficking #helpthemheal #stopthepain #diasporafoundation #diasporasocialmedia |
|
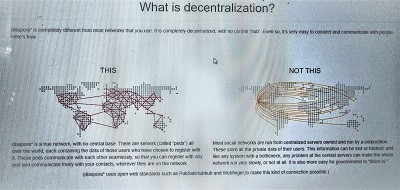
There is no question the effects that social media has on the “business” of human trafficking and as social media and technology evolve in tandem so do the skills and resources of traffickers. Traffickers are now networked through certain platforms, to include Facebook, Instagram as well as the many elements of the dark web in which they operate relatively “under the radar” of law enforcement. Traffickers have become more emboldened by the ability to conduct recruiting, grooming and the “selling” of their victims using these sources which sometimes causes their own demise and that is a good thing because they can feel invulnerable to discovery and make mistakes. That being said, there is a vast network of like minded evil people that span the globe and no doubt, watch out for each other as they share resources on how to not get caught. We all know the usual platforms used by traffickers to conduct their “business” and they are constantly being monitored by some of the best investigators in the world but there are so many that it is virtually impossible to find, track and monitor all of them despite the enormous efforts of law enforcement. These evil people find, use and know how to manipulate these platforms to their advantage using remote servers, routing their activities through a wide network of IP addresses and many other “tricks of the trade”. Resources such as the dark web pride themselves in ensuring their users secrecy and anonymity by strategically hiding their information such as IP addresses and do not require people to use real information. This allows traffickers to use a variety methods to operate relatively undetected for a significant amount of time and makes it difficult for investigators to lock down locations and activities. The massive growth in the use of social media by our youth which often times is haphazard at best, has opened many doors to conniving traffickers that cue in on certain posts and key words that kids use, especially when they openly state they are feeling useless, unloved, and that nobody cares about them or what happens to them. Traffickers will not hesitate to reach out posing as like minded and similar aged individuals that either claim to feel the same or offer a refuge of sorts, telling them that they are “here” for them to vent and promise their potential victims that they care about them and that they can have a better life, which we all know is the farthest thing from the truth. One of the main benefits to traffickers is that their victims have no way of truly finding out who they are communicating with until it is already too late. They “bait” their potential victims ensuring them that if they stick with the trafficker, they will get the love and respect they deserve. Traffickers coax their potential victims into moving to a more secure platform to communicate to “hide” their conversations from the prying eyes of parents and others that may “interfere” with their growing “relationship”. This allows for a more open discussion where the trafficker continues to “empathize”, in reality, they are taking them to a dark and unfiltered place to communicate. Once they are fully engulfed into this new world full of possibilities and comfortable with their “rescuer” they become more relaxed and trusting as the trafficker continues to build them up and ensure them that are “safe” and that no one will get in the way of their “relationship”. Once the potential victims are in the grasp of the trafficker and an unquestionable level of trust is built, it can turn into an intimate relationship where lewd photos are requested and the unsuspecting victim is inclined to oblige sometimes as they think their “rescuer” is of the same age and there is no harm in doing so. This is when the trafficker feels they “have them” and at the first sign of their victim wanting to distance themselves from the trafficker for whatever reason, they will not hesitate to begin using these photos as blackmail telling them that the photos will be sent to families and friends as well as blasted all over social media. To a child that already feels unloved and disrespected, this is detrimental to them and they feel trapped because this would surely make things worse in their personal life if these photos get out so they feel there is no other option than to continue with the “relationship”. One such platform that traffickers may be using and I was recently made aware of is, https://diasporafoundation.org/, I do not have any significant proof of what this organization has operating on their platform but it surely offers privacy to their users that, from their website, seems to be a recipe to allow traffickers and child predators to operate with significant secrecy. These types of platforms, while with possibly good intentions to ensure privacy for their users, are a safe haven for evil to thrive undetected. Here is some of what they offer directly from their site; - Be who you want to be - A lot of networks insist that you use your real identity. Not diaspora*. Here you can choose who you want to be, and share as much or as little about yourself as you want. It really is up to you how you want to interact with other people. - Host it yourself- Choose where your data are stored by choosing a pod you’re happy with. If you want to be really secure, you can set up and host your own pod on servers you control, and interact only with pods you trust, so no one can get at your personal data. What can we do to decrease the chances of our children becoming victims to this evil? Well, while it may seem next to impossible, the solutions are relatively simple but it requires vigilance, understanding of your child's needs and mindset, it requires we, as parents to respectfully monitor our youth's social media activity. We must be completely honest with them about the threats that exist and educate them on the signs of a potential predator/trafficker and their methods, this requires education on the topic. I fully understand this topic is scary and taboo but in order for us to protect our children, as with any threat, we must accept the reality, understand it and fight it at every step. If you are honest with your children about this they may respect you more for telling them the truth and will thank you especially if they later see or hear something they raises an alarm. You must explain to them, in simple terms that they can relate to, why you need to monitor, without being invasive, their social media use, don't be sneaky about it, do it with them present as this will display to them that you trust them and respect their privacy. Do not dive in more that what you tell them you are going to do, come up with a plan and present it to them. In conclusion, many times children seek refuge using the ear of another when they feel unloved, unwanted and disrespected so it is our responsibility as a parent, guardian and family member, and we owe it to them, to ensure our youth feel unquestionable and unconditional love, caring and respect and let them know that you are willing to listen to them and not just pushing them off onto the internet. Children should not feel “forced” to seek guidance and refuge from an outside source that is truly unknown, they should feel comfortable enough with their parents/guardians and other family members to speak openly about their concerns and feelings. Be open, be honest, be caring and respectful and let them know that you are only trying to protect them from the unknowns and that “Evil People Will Push The Limits of Evil Deeds to Feed Their Sick Addiction and Greed” | |